Security is complex, managing it doesn’t have to be.
Today’s reality is that every network needs a full arsenal of scanning engines to protect against spyware, viruses, malicious apps, and data leakage – all the way through ransomware, botnets, advanced persistent threats, and zero day malware. A true network security solution will address all aspects of threat prevention, detection, correlation, and response not just as they stand today, but also as those threats evolve.
BlackCSI’s Total Security solution provides the most complete suite of unified security controls, consistently addressing new and evolving network threats including, but not limited to, advanced malware and ransomware.
All businesses, regardless of size, need to pay attention to performance.
Slow security scanning times can cripple a network’s ability to handle high-volume traffic. Some companies are even forced to decrease protection to keep performance strong, but BlackCSI’s Total Security will never make you choose between security and speed. Leveraging the power of multi-core processing, BlackCSI’s platform is engineered to deliver the fastest throughput when it matters – with all security controls turned on. Total Security can run all scanning engines simultaneously for maximum protection while still maintaining your processes at the blazing fast speeds your business requires.
Critical decisions about security often need to be made quickly.
You need to know what’s happening not just in the network, but on your devices inside and outside the firewall as well.Total Security’s Threat Detection and Response provides continuous event monitoring, detection and remediation of threat activity on the endpoint. This data is taken from all devices across your network and presented as immediately actionable information. Using these tools, BlackCSI can identify behavioral trends, pinpoint potential network threats, block inappropriate use, monitor network health, and much more.
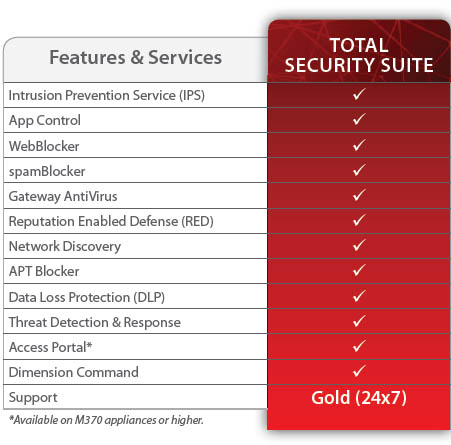
BlackCSI’s Total Security also includes all of the services your business needs to be secure - including advanced malware protection, data loss protection, enhanced network visibility capabilities, a secure access portal, and the ability to take action against threats right from our network visibility platform.
For more information, or to find out if your network is secure, contact us today!
Intrusion Prevention Service
IPS uses continually updated signatures to scan traffic on all major protocols to provide real-time protection against network threats, including spyware, SQL injections, cross-site scripting, and buffer overflows
Application Control
Selectively allow, block, or restrict access to applications based on a user’s department, job function, and time of day and to then see, in real-time, what’s being accessed on your network and by whom.
WebBlocker URL Filtering
In addition to automatically blocking known malicious sites, WebBlocker’s granular content and URL filtering tools enable you to block inappropriate content, conserve network bandwidth, and increase employee productivity.

SPAMBlocker
Real-time spam detection for protection from outbreaks. Our spamBlocker is so fast and effective, it can review up to 4 billion messages per day.
Gateway Antivirus
Leverage our continuously updated signatures to identify and block known spyware, viruses, trojans, worms, rogueware and blended threats – including new variants of known viruses. At the same time, heuristic analysis tracks down suspicious data constructions and actions to make sure unknown viruses don’t slip by.
Reputation Enabled Defense
A powerful, cloud-based reputation lookup service that protects web users from malicious sites and botnets, while dramatically improving web processing overhead.
APT Blocker - Advanced Malware Protection
APT Blocker uses a next-gen sandbox to detect and stop the most sophisticated attacks including ransomware, zero day threats and other advanced malware.

Data Loss Protection
This service prevents accidental or malicious data loss by scanning text and common file types to detect sensitive information attempting to leave the network.

Threat Detection and Response
Correlate network and endpoint security events with enterprise-grade threat intelligence to detect, prioritize and enable immediate action to stop malware attacks. Improve visibility by evolving your existing security model to extend past prevention, to now include correlation, detection and response.

Access Portal
Access Portal provides central location for access to cloud-hosted applications, and secure, clientless access to internal resources with RDP and SSH.

Dimension Command
Dimension translates data collected from all appliances across your network into actionable network and threat intelligence. Dimension Command gives you the power to take action to mitigate those threats instantly, from one central console.